The articulation of the requirement is the most important part of the process, and it seldom is as simple as it might seem. There should be a dialogue concerning the requirement, rather than a simple assertion of need. Perhaps the customer knows precisely what is needed and what the product should look like. Perhaps... not. Interaction is required: discussion between ultimate user and principal producer. This is often difficult due to time, distance, and bureaucratic impediments, not to mention disparities of rank, personality, perspectives, and functions. 25
Defining the Intelligence Problem
Customer demands, or "needs," particularly if they are complex and time-sensitive, require interpretation or analysis by the intelligence service before being expressed as intelligence requirements that drive the production process.26 This dialog between intelligence producer and customer may begin with a simple set of questions, and if appropriate, progress to a more sophisticated analysis of the intelligence problem being addressed.
The "Five Ws" - Who, What, When, Where, and Why - are a good starting point for translating intelligence needs into requirements. A sixth related question, How, may also be considered. In both government and business, these questions form the basic framework for decision makers and intelligence practitioners to follow in formulating intelligence requirements and devising a strategy to satisfy them. Typically, government intelligence requirements are expressed in terms of foreign threats to national or international security. In business, requirements may be expressed in terms of the competitor’s standing in the marketplace in comparison to one’s own posture. Representative examples from each sector follow:
 |
Examination of these basic scenarios should inspire further development of the concept of determining customer needs in specific situations. The thoughtful researcher may pro-pose, for example, ways to gather information on additional aspects of the problem (Who, What) and on customers (Who), as well as on the attendant motivations (Why) and strategies (How) of the target and the customer. Defining the intelligence problem in this manner paves the way for the next step in the intelligence process - the development of intelligence collection, analysis, and production requirements, explained later in this chapter.
Another, more complex model for defining intelligence scenarios employs the Taxonomy of Problem Types.27 The table below illustrates the factors that customers and producers may take into account in articulating the nature of the intelligence problem and selecting a strategy for resolving it.
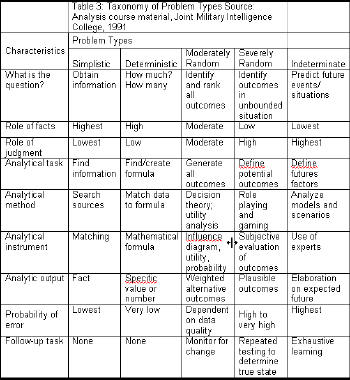 |
As with the "Five Ws," this model enables decision makers and analysts to assess their needs and capabilities in relation to a particular intelligence scenario. This ability to establish a baseline and set in motion a collection and production strategy is crucial to conducting a successful intelligence effort. Too often, both producers and customers waste valuable time and effort struggling to characterize for themselves a given situation, or perhaps worse, they hastily embark upon an action plan without determining its appropriateness to the problem. Employing a structured approach as outlined in the Taxonomy of Problem Types can help the players avoid these inefficiencies and take the first step toward generating clear intelligence requirements by defining both the intelligence problem and the requisite components to its solution. Following are example scenarios. The reader is encouraged to follow the scenarios down the columns of the taxonomy table, then generate new scenarios in similar fashion.
Intelligence Problem Definition
A Government Scenario
The Severely Random problem type is one frequently encountered by the military in planning an operational strategy. This is the realm of war gaming. The initial intelligence problem is to identify all possible outcomes in an unbounded situation, so that commanders can generate plans for every contingency. The role of valid data is relatively minor, while the role of judgment is great, as history and current statistics may shed little light on how the adversary will behave in a hypothetical situation, and the progress and outcome of an operation against that adversary cannot be predicted with absolute accuracy. Therefore, the analytical task is to define and prepare for all potential outcomes. The analytical method is role playing and war gaming: placing oneself mentally in the imagined situation, and experiencing it in advance, even to the point of acting it out in a realistic setting. After experiencing the various scenarios, the players subjectively evaluate the outcomes of the games, assessing which ones may be plausible or expected to occur in the real world. The probability of error in judgment here is inherently high, as no one can be certain that the future will occur exactly as events unfolded in the game. However, repeated exercises can help to establish a measure of confidence, for practice in living out these scenarios may enable the players to more quickly identify and execute desired behaviors, and avoid mistakes in a similar real situation.
A Business Scenario
The Indeterminate problem type is one facing the entrepreneur in the modern telecommunications market. Predicting the future for a given proposed new technology or product is an extremely imprecise task fraught with potentially dire, or rewarding, consequences. The role of valid data is extremely minor here, whereas analytical judgments about the buying public’s future - and changing - needs and desires are crucial. Defining the key factors influencing the future market is the analytical task, to be approached via the analytical method of setting up models and scenarios: the if/then/else process. Experts in the proposed technology or market are then employed to analyze these possibilities. Their output is a synthesized assessment of how the future will look under various conditions with regard to the proposed new product. The probability of error in judgment is extremely high, as the decision is based entirely on mental models rather than experience; after all, neither the new product nor the future environment exists yet. Continual reassessment of the changing factors influencing the future can help the analysts adjust their conclusions and better advise decision makers on whether, and how, to proceed with the new product.
Generating Intelligence Requirements
Once they have agreed upon the nature of the intelligence problem at hand, the intelligence service and the customer together can next generate intelligence requirements to drive the production process. The intelligence requirement translates customer needs into an intelligence action plan. A good working relationship between the two parties at this stage will determine whether the intelligence produced in subsequent stages actually meets customer needs. However, the differing perspectives that each side brings to the negotiation process can make cooperation between them a difficult feat.28
Customers want intelligence to guide them clearly in making policy and operational decisions. They may have little understanding of the intelligence process, and little patience for the subjectivity and conditionality of intelligence judgments. For customers, intelligence can be just one of many influences on their decision-making, and may be given little weight in comparison to other, more readily digested, familiar, or policy-oriented inputs. However, intelligence is neither designed nor equipped to meet these customer expectations.29 As a discipline, intelligence seeks to remain an independent, objective advisor to the decision maker. The realm of intelligence is that of "fact," considered judgment, and probability, but not prescription. It does not tell the customer what to do to meet an agenda, but rather, identifies the factors at play, and how various actions may affect outcomes. Intelligence tends to be packaged in standard formats and, because of its methodical approach, may not be delivered within the user’s ideal timeframe. For all these reasons, the customer may not see intelligence as a useful service.30
Yet, somehow the intelligence producer and customer must reconcile their differing perspectives in order to agree on intelligence requirements and make the production process work. Understanding each other’s views on intelligence is the first step toward improving the relationship between them. The next step is communication. Free interaction among the players will foster agreement on intelligence priorities and result in products that decision makers recognize as meaningful to their agendas, yet balanced by rigorous analysis.31 In addition, as discussed below, customer feedback on production quality will lead to better definition of future intelligence problems and requirements.
Types of Intelligence Requirements
Having thus developed an understanding of customer needs, the intelligence service may proactively and continuously generate intelligence collection and production requirements to maintain customer-focused operations. Examples of such internally generated specifications include analyst-driven, events-driven, and scheduled requirements. The table below briefly describes them.32
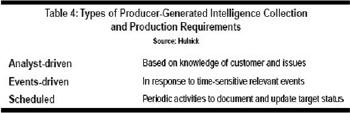 |
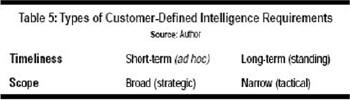
Further distinctions among intelligence requirements include timeliness and scope, or level, of intended use. Timeliness of requirements is established to meet standing (long-term) and ad hoc (short-term) needs. When the customer and intelligence service agree to define certain topics as long-term intelligence issues, they generate a standing requirement to ensure that a regular production effort can, and will, be maintained against that target. The customer will initiate an ad hoc requirement upon realizing a sudden short-term need for a specific type of intelligence, and will specify the target of interest, the coverage timeframe, and the type of output desired.
The scope or level of intended use of the intelligence may be characterized as strategic or tactical. Strategic intelligence is geared to a policymaker dealing with big-picture issues affecting the mission and future of an organization: the U.S. President, corporate executives, high-level diplomats, or military commanders of major commands or fleets. Tactical intelligence serves players and decision makers "on the ground" engaged in current operations: trade negotiators, marketing and sales representatives, deployed military units, or product developers.
 |
Ensuring that Requirements Meet Customer Needs
Even when they follow this method of formulating intelligence requirements together, decision makers and their intelligence units in the public and private sectors may still have an incomplete grasp of how to define their needs and capabilities - until they have evaluated the resultant products. Thus, customer feedback, production planning and tasking, as well as any internal product evaluation, all become part of the process of defining needs and creating intelligence requirements. However, when intelligence producers and users are not in nearly direct, daily contact, this process can consume a good deal of time. This is why the national Intelligence Community is experimenting with compressing both the accustomed time and spatial dimensions of the intelligence process through remote electronic collaboration and production methods.33
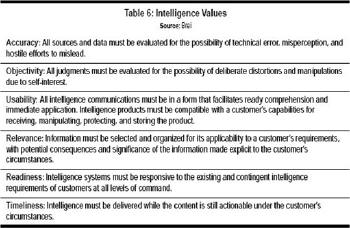
Whether in business or government, six fundamental values or attributes underlie the core principles from which all the essential intelligence functions are derived. The corollary is that intelligence customers’ needs may be defined and engaged by intelligence professionals using these same values. Table 6 offers a brief explanation of how both intelligence customers and producers may use these values to evaluate how well they have translated needs into requirements that will result in useful products.34
Interpretation of these values turns a customer’s need into a collection and production requirement that the intelligence service understands in the context of its own functions. However, illustrating the complexity of the intelligence process, once this is done, the next step is not necessarily collection.
Rather, the next stage is analysis. Perhaps the requirement is simply and readily answered - by an existing product, by ready extrapolation from files or data bases, or by a simple phone call or short desk note based on an analyst’s or manager’s knowledge. On the other hand, the requirement might necessitate laborious effort - extrapolation, collation, analysis, integration, and production - but still the product can be constructed and sent directly to the requester. Case closed; next problem.... Preliminary analysis might well show, however, that while much data exists, because the issue at hand is not a new one, gaps in information must be filled. Obviously, this calls for collection. This brings up an essential point: consumers do not drive collection per se; analysts do - or should.35 Part III explores this next step in the intelligence process.
 |
Glossary
| ASD/C4ISR | Assistant Secretary of Defense for Command, Control, Communications, Computers, Intelligence, Surveillance and Reconnaissance |
| BI | Business Intelligence |
| CIA | Central Intelligence Agency |
| CISS | Center for Information Systems Security |
| CSRC | Computer Security Resource Center |
| DCI | Director of Central Intelligence |
| DIA | Defense Intelligence Agency |
| DII | Defense Information Infrastructure |
| DISA | Defense Information Systems Agency |
| DoD | Department of Defense |
| DODSI | Department of Defense Security Institute |
| FISINT | Foreign Instrumentation and Signature Intelligence |
| GPO | U.S. Government Printing Office |
| HUMINT | Human Intelligence |
| IC | Intelligence Community |
| IITF | Information Infrastructure Task Force |
| IMINT | Imagery Intelligence |
| INFOSEC | Information Systems Security |
| INFOWAR | Information Warfare |
| IOSS | Interagency OPSEC Support Staff |
| IPMO | INFOSEC Program Management Office |
| ISSR-JTO | Information Systems Security Research Joint Technology Office |
| JIVA | Joint Intelligence Virtual Architecture |
| JMIC | Joint Military Intelligence College |
| MASINT | Measurement and Signature Intelligence |
| MBTI | Myers-Briggs Type Indicator |
| MRI |
Management Research Institute |
| NACIC | National Counterintelligence Center |
| NCSC | National Computer Security Center |
| NIC |
National Intelligence Council |
| NII | National Information Infrastructure |
| NIMA | National Imagery and Mapping Agency |
| NIST | National Institute for Standards and Technology |
| NSA | National Security Agency |
| NSTISSC | National Security Telecommunications and Information Systems Security Committee |
| NTIA | National Telecommunications and Information Administration |
| OMB |
Office of Management and Budget |
| OPSEC | Operations Security |
| OSD | Office of the Secretary of Defense |
| OTP | Office of Technology Policy |
| SCIP | Society of Competitive Intelligence Professionals |
| SIGINT | Signals Intelligence |
References
25 Dearth, "National Intelligence," 17-18.
26 Dearth, "National Intelligence," 18.
27 Morgan D. Jones, The Thinker’s Toolkit (New York: Random House, 1995), 44-46, as elaborated by Thomas H. Murray, Sequoia Associates, Inc., Arlington, VA., in coursework at the Joint Military Intelligence College.
28 Arthur S. Hulnick, "The Intelligence Producer-Policy Consumer Linkage: A Theoretical
Approach," Intelligence and National Security, 1, No. 2, (May 1986): 214-216.
29 Hulnick, "Producer-Policy Consumer Linkage," 215-216.
30 Hulnick, "Producer-Policy Consumer Linkage," 216.
31 Adapted from Michael A. Turner, "Setting Analytical Priorities in U.S. Intelligence," International Journal of Intelligence and CounterIntelligence, 9, No. 3, (Fall 1996): 320-322.
32 Adapted from Arthur S. Hulnick, "Managing Intelligence Analysis: Strategies for Playing the End Game," International Journal of Intelligence and CounterIntelligence 2, No. 3 (Fall 1988):
327.
33The U.S. military has pioneered the concept of an electronic intelligence operating environment that transcends organizational boundaries. Congress has recommended that the IC adopt this Joint Intelligence Virtual Architecture model to take advantage of technological developments, reduce bureaucratic barriers, and thereby provide policymakers with timely, objective, and useful intelligence. See U.S. Congress Staff Study, House Permanent Select Committee on Intelligence, IC21: The Intelligence Community in the 21st Century, (April 1996): Section III, "Intelligence Requirements Process."
34 The six values are adapted by Brei from an earlier version of U.S. Department of Defense, Joint Chiefs of Staff, Joint Pub 2-0, Joint Doctrine for Intelligence Support to Operations (Washington, DC: GPO, 5 May 1995), IV-15.
35 Dearth, "National Intelligence," 18-19.