So, the LI and DOD newsletters will explore the world of amateur spying in the next several issues. With the average person using Google maps and other resources available on the Web, electronic media and in print, it seemed like a good idea to challenge our readers to look into some of the techniques that extend or supplement their existing location intelligence skills. The general frame we have in mind is to look at imagery, communications, search basics, spy technology and other subjects that can help you get started as an amateur spy.
I am not sure we will expose any deep and dark secrets, but we may have a little fun and adventure.
Of course, there is always the possibility that as amateur spies we may acquire some new skill sets that may help us in what has become a very different environment than what existed in the old 20th century. Being a spy, amateur or professional, is really the application of a logical process to the acquisition of knowledge. Conversely, if you know how to acquire knowledge, it would follow that you would understand how to keep others from finding out things about you or your enterprise.
We all know that there are spies out there - people lurking in the shadows, trying to steal corporate secrets, get deep into your computer and acquire your passwords and maybe even locate your secret family recipe for chocolate chip cookies.
But a great deal of spying is not whimsy or games. We are all attacked by spyware, phishing or other intrusions for unpleasant purposes. As part of the information gathering for this series of spy adventures, I spoke with Kevin Coleman, who has authored a number of articles in Directions Media about intelligence, homeland security and related topics. He directed me to the website www.spy-ops.com, which has a downloadable file about the effect of corporate espionage. The scope of this form of spying is astonishing. To quote from the abstract in this brief (pdf):
Corporate espionage is the dirty little secret of global business. Espionage activities are often masked under the title of competitive intelligence. But in the end, thieves or spies still acquire sensitive, restricted information assets of another entity, which may include product designs, business models, marketing plans, research and development files, customer lists, employee lists, pricing strategies and other intellectual property.Take a look at this chart from this same Spy-Ops Training brief.
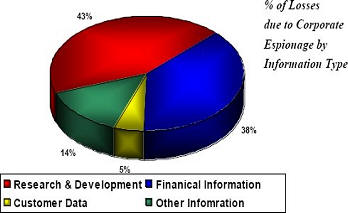
The Spy-Ops data shows 43% of loss is in the research and development area, including new products, methods and proprietary processes. Financial information is also on the high end. One factoid from this same brief - in 1999 (old low tech last century) the FBI and the US Chamber of Commerce estimated that companies were losing $2 million a month to corporate espionage, and this is growing. You can’t help but wonder what that number might be today.
In today’s world, with all kinds of spy-like activities going on, maybe a little exposure to the techniques, methodologies and mechanics of basic spy craft would be a good thing to know. You probably aren’t going to become James Bond or Mata Hari, but we should have some fun, learn a few things and, at the very least, be able to use covert contact phrases with each other. All levity aside, the key point is that if you don’t learn some spy craft, you will very likely be the victim of someone who has.
So go find that old shortwave radio, dig up your old trench coat and generic briefcase, and remember, Uncle Otto from Munich sends greetings.