Unifly And Nexova Finish Esa Navisp Work on Cyber-resilient U-space Operations

Unifly, working alongside Nexova, has wrapped up Phase I of SecureUTM 2 under the European Space Agency’s NAVISP program, with the effort centered on reducing the impact of GNSS jamming and spoofing on modern drone activity.
The result is a certification-aware, risk-led cybersecurity base for secure, durable, and scalable unmanned traffic management and U-space services across Europe.
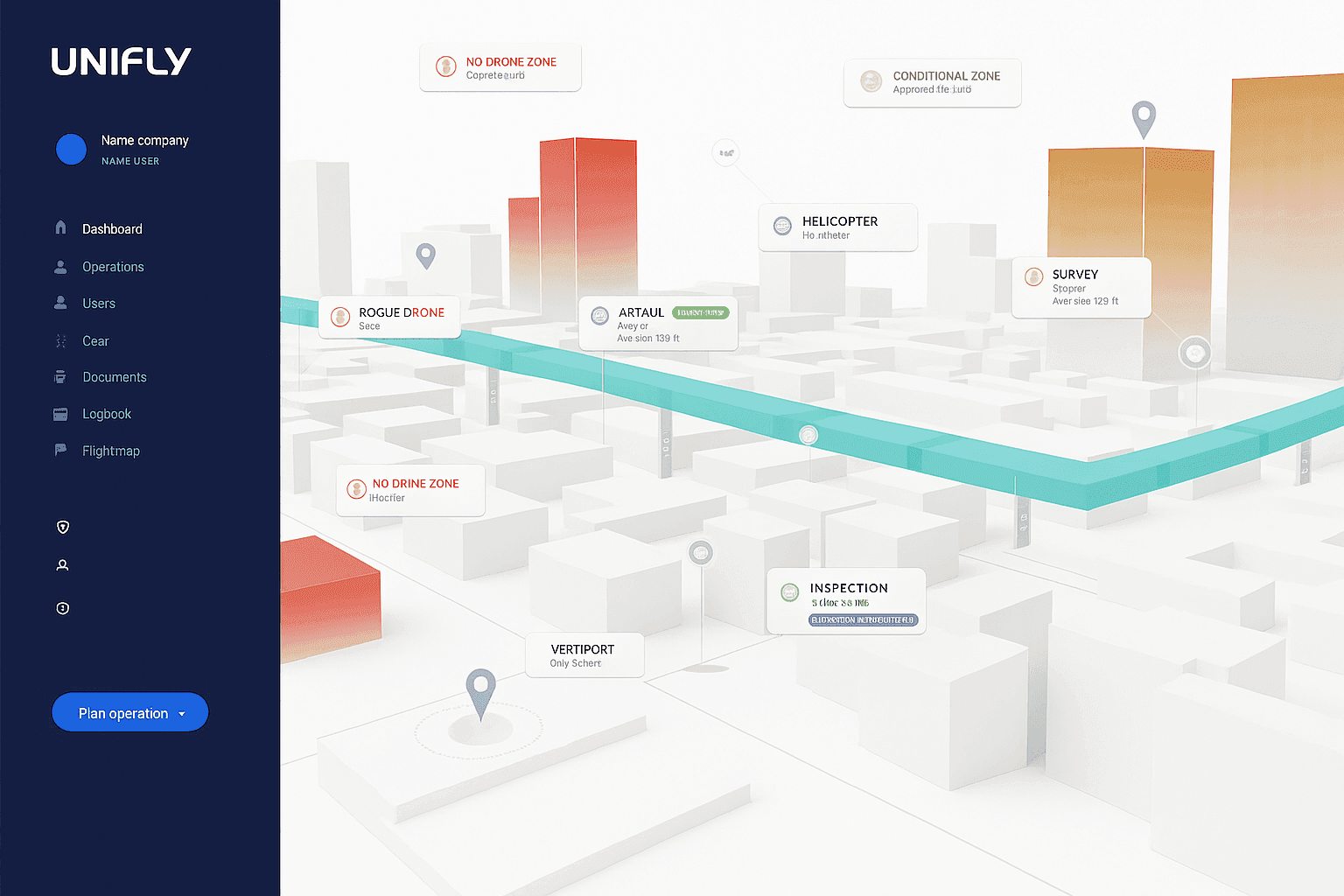
As drone missions become more demanding and move across national boundaries, cybersecurity is no longer a side topic. It now sits close to operational continuity, public confidence, and safe airspace management. SecureUTM 2 builds security engineering into the underlying UTM architecture itself, aligning the work with European U-space regulation, Common Criteria methods, and ENISA risk frameworks. In practice, Unifly’s platform is the software layer used to coordinate, monitor, and authorize drone operations in shared airspace, helping service providers and authorities manage flight requests, airspace data, conformance monitoring, and system-to-system exchanges. That support for U-space is tied directly to European requirements around digital coordination, traceability, and safer integration of drones into managed airspace, rather than being treated as a standalone security add-on. From what I’ve seen in complex infrastructure projects, that kind of early design discipline matters far more than a late compliance patch. It is a bit like cleaning GPS data at the source instead of trying to correct a bad track after the flight.
In simple terms, UTM for drones is the set of digital services that helps organize unmanned aircraft operations, especially when many flights, operators, and airspace constraints have to be handled at once. It covers functions such as flight authorization, tracking, identification, conflict handling, and information sharing. ATM, or Air Traffic Management, serves the broader aviation system and is built mainly around crewed aircraft, airports, and conventional air navigation services. UTM is narrower and drone-focused, but it has to connect with ATM when unmanned and crewed traffic share the same operational picture.
Building on the earlier SecureUTM 1 work, Phase I of SecureUTM 2 materially broadened the cybersecurity baseline for UTM systems. The main deliverables included the following:
- A more unified Protection Profile for UTM environments
- An updated Security Target for the Unifly platform
- A structured risk review paired with certification-focused gap analysis
- A secure architectural starting point designed for real-world U-space complexity
- A proof-of-concept testbed setup
Risk-Led Engineering Priorities
A requirement-by-requirement gap review turned the security findings into a prioritized implementation roadmap. When I looked through the structure, it read much like a layered GIS assessment, where each control only makes sense when you see how it connects to the rest of the system, the data flow, and the operational infrastructure.
The roadmap highlights these areas:
- Authentication of PNT sources and plausibility validation
- Stronger session integrity and transport-layer protection
- Resilience against denial-of-service events
- Device-level authentication and auditing
- Protected storage and encryption measures
This methodical approach supports actual deployment while also moving the platform toward future EU cybersecurity certification readiness. In practical terms, that matters for operators, an air navigation service provider, and the wider aviation ecosystem that depends on trustworthy data, clear management processes, and resilient digital interfaces, including API-based system exchanges.
For users, the benefit is fairly direct: a stronger UTM platform can improve flight approval workflows, increase visibility across active operations, reduce the impact of interference or faulty positioning data, and give regulators and service providers more confidence in how drone traffic is being managed. Key platform functions in that context include airspace coordination, mission authorization, real-time monitoring, conformance checks, alerting, and integration with external aviation systems.
Tested Defenses for GNSS and PNT Interference
Phase I put particular weight on GNSS jamming and spoofing, both of which are showing up more often in unmanned aerial vehicle operations. Those threats can affect navigation, flight planning, aircraft tracking, and situational awareness across shared airspace. In a mixed environment that may involve airport proximity, radar inputs, air traffic control coordination, and remote aircraft pilot decision-making, signal integrity becomes foundational.
To address that, the team validated practical, layered mitigations through a dedicated U-space proof-of-concept testbed using Hardware-in-the-Loop UAV simulations. I tend to trust this kind of setup more than abstract claims alone. In my own testing habits, if I can check a system across three or four conditions and see the data line up consistently, confidence goes up fast.
The validated measures include:
- Onboard detection of GNSS jamming
- Fleet-level inference of interference patterns
- Monitoring for trajectory plausibility and conformance
- OSNMA-based verification of messages
- Structured anomaly logging and alerting
The testbed gives the project a repeatable way to simulate attacks, evaluate performance against KPIs, and generate evidence suitable for regulators. That kind of repeatability is important. It turns cybersecurity from a one-off checklist into something closer to managed air navigation quality control.
Groundwork for Phase II and Wider European Use
Beyond the immediate security controls, Phase I also produced a structured blueprint for the U-space testbed, along with verification methods and digital twin foundations that can support ongoing validation, operator training, and continuous cybersecurity testing. I reviewed similar validation frameworks before, and the useful ones usually make it easier to compare one flight scenario against another in a clean, trackable way, almost like working across aligned map layers.
SecureUTM 2 also supports Belgium’s approach to U-space deployment and reinforces the country’s role in secure drone integration across European aviation infrastructure.
At the article level, the work highlights Unifly’s practical role more than its corporate profile. The company’s CEO, broader partnership network, awards history, and other collaborations are not identified in the material covered here, so those details are not part of this project summary. What is clear is that the effort itself is collaborative, with Unifly and Nexova working under ESA NAVISP toward a more secure operational base for European U-space services.
In application terms, that kind of platform can support urban drone delivery trials, emergency response flights, infrastructure inspection, airport-adjacent operations, and other missions where multiple operators need a shared, trusted view of airspace activity. Phase II is expected to concentrate on putting the prioritized controls into operation, broadening validation capabilities, and tightening alignment with EU certification frameworks. For aircraft operators, service platforms, and the systems that connect airspace users with management tools, that next step is where the architecture starts proving itself under real operational pressure.




